Effective May 21, 2023, P&N has joined EisnerAmper. Read the full announcement here.

Employees can pose a significant risk to your cybersecurity posture. What happens when an internal user plays a critical role in a hack or cybersecurity breach?
The Department of Homeland Security National Cybersecurity and Communications Integration Center (CISC) states “insider threats, to include sabotage, theft, espionage, fraud, and competitive advantage are often carried out through abusing access rights, theft of materials, and mishandling physical devices.” 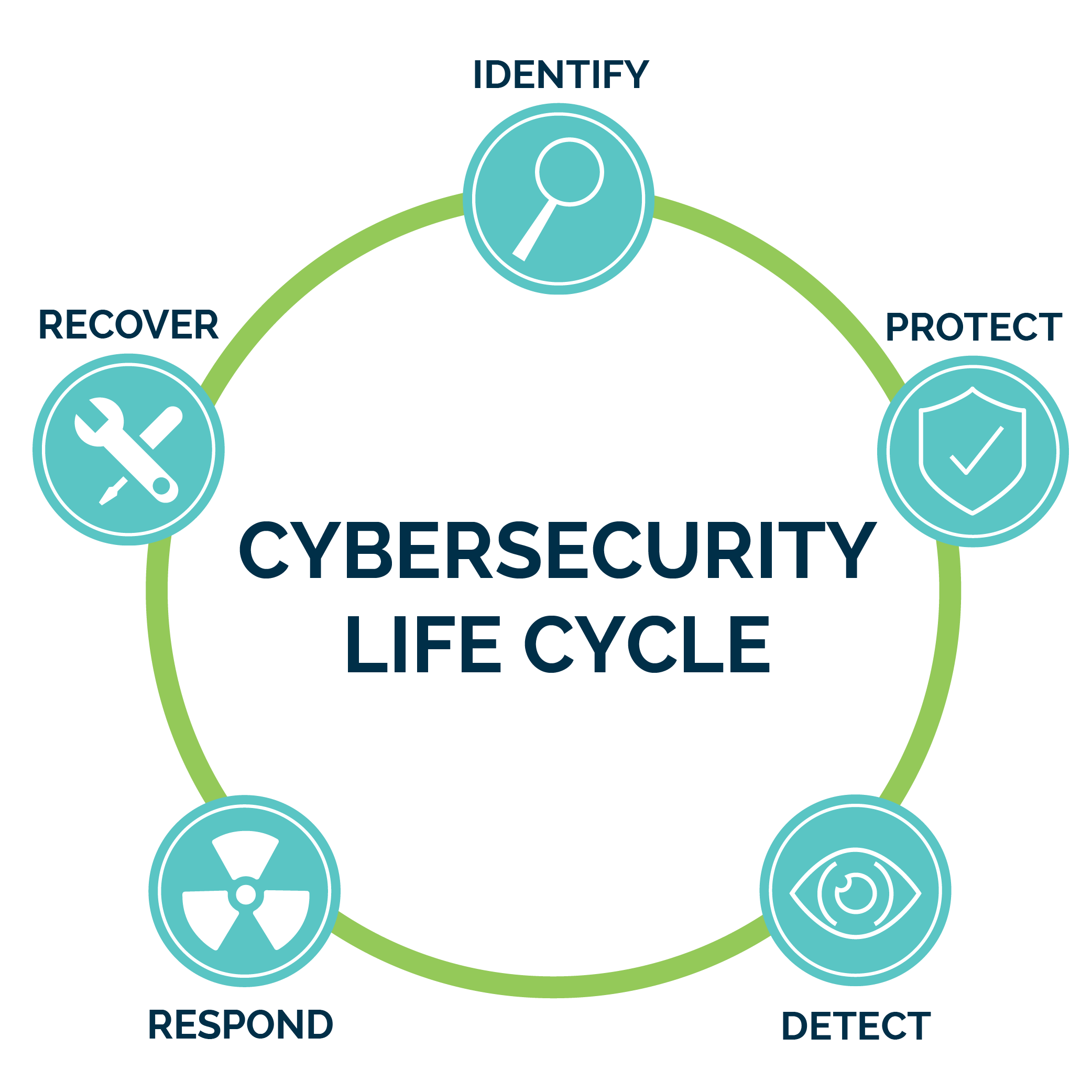
The current Verizon Data Breach Investigation Report finds that outside threats leverage stolen credentials in 35% of attacks, followed closely by phishing/malware emails. The third major cause of breaches is user error. The implication of this finding is that a significant portion of security hardening efforts can be rendered ineffective by the very people who need access to an organization's data, facilities, and systems. This category is not limited to employees: anyone who has been granted access at some level can erode security. Current and former employees, vendors, contractors, and suppliers should all be considered potential insider threats.
Negligent Insider Threats
While authorized access to company applications and data is necessary for a variety of roles, users might unknowingly and negligently expose sensitive information by:
- Using an unapproved file sharing application like Dropbox or Box;
- Emailing work files from a personal email account; or,
- Screen-sharing sensitive content in a collaboration tool like Zoom, Cisco WebEx, or Microsoft Teams.
The vast majority of breaches from insiders can be attributed to lack of knowledge, inadequate training, or even simply a sense of urgency to provide assistance when asked, leading an employee to bypass controls or access and share data through unapproved means.
To counter this type of threat, you must create a healthy culture that educates users and rewards a positive security attitude.
Cyber incidents can also arise from employee recklessness or procedural violations that provide system access to threat actors. Unfortunately for most companies, these types of end-user activities typically endure over a significant period, and happen in many work environments, particularly in higher education, healthcare, financial, legal, and governmental organizations.
To counter threats stemming specifically from negligent insiders, you must create a healthy culture that educates users and rewards a positive security attitude. Some effective tactics to employ include:
- Implementing immersive, continual, and job-specific training to improve employee recognition of phishing and other social threats;
- Ensuring that security tools are fully-adopted and easily-leveraged;
- Reviewing user-facing software systems for ease-of-use to limit human error; and,
- Maintaining staff values and attitudes that align with organizational mission and ethics.
Malicious Insider Threats
Although different in motive, the malicious insider poses no less threat than a negligent insider. Malicious insiders seek to monetize corporate data or intellectual property. Some malicious insiders may even be working for nation states or organized crime. Identifying the activities that indicate a malicious insider threat exists may be difficult, but there may be non-technical red flags that provide an indication something is not right. The CISC has provided the following behavioral characteristics that can be used as indicators:
- Remotely accesses the network while on vacation, sick, or at odd times;
- Works odd hours without authorization;
- Notable enthusiasm for overtime, weekend, or unusual work schedules;
- Unnecessarily copies material, especially if it is proprietary or classified;
- Interested in matters outside of the scope of their duties;
- Shows signs of vulnerability, such as drug or alcohol abuse, financial difficulties, gambling, illegal activities, poor mental health, or hostile behavior; and,
- Other warning signs such as the acquisition of unexpected wealth, unusual foreign travel, or unexpected absences.
Protection and Detection
To counteract these threats, whether malicious or negligent, a combination of social and technical preventive and detective activities should be implemented:
- Install and configure data loss prevention and data rights management solutions;
- Implement effective security technologies and procedures (e.g., enhanced detection and response, multi-factor authentication, etc.);
- Ensure system-wide logging to gain visibility and detective capabilities on high outbound traffic systems (data exfiltration);
- Use positive reinforcement in social engineering training and detection;
- Require authentication and authorization for all IT assets (e.g., access cards, passwords, network access control, etc.);
- Implement and publicly reveal the use of monitoring systems that record network traffic, USB storage activity, printing activities, and unapproved encryption use;
- Gain visibility by implementing a SIEM or other log analysis engine in conjunction with custom-tuned logs for your environment;
- Provide employee feedback mechanisms to give employees the ability to voice concerns and frustrations and to assist in neutralizing certain forms of the insider threat;
- Institute recognition programs that offer commendations to assist in mitigating the ego-motivated insider threat;
- Authorize users based on least-privileged access and conduct periodic audits to detect inappropriately-granted access or access that still exists from previous job roles/functions and should be removed.
Due to the cybersecurity environment we operate in today, no one can guarantee 100% success in preventing all attacks. Ultimately, a holistic approach that incorporates both protective and detective technologies, coupled with novel approaches to data security, like zero trust, can help mitigate the risks to an acceptable threshold balanced with your organization's investment of time, money, and effort.
Learn More
Experienced P&N Technology Services professionals work diligently to develop informative articles and webinars on a wide variety of topics, such as:
- How can you stay current in an always-evolving threat environment?
- What steps must be taken to integrate new technology into a secure infrastructure?
- What strategies can help you identify vulnerabilities before attackers can establish a foothold?
- What initial steps should your organization take if current security measures aren't enough to protect against an attack?
- How should your organization respond to a data breach?
Join our cybersecurity contact list to stay updated on all P&N technology insights and webinars.




